Icebergs, The Nordics, and Other BYOD Considerations
February 13, 2013 1 Comment
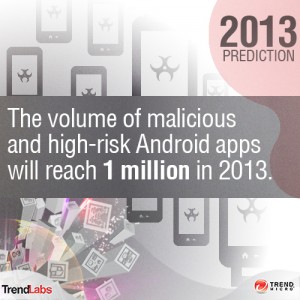
 New data shows that companies are increasingly exposed to security risks due to a variety of consumer-grade technology brought in by the employees.
New data shows that companies are increasingly exposed to security risks due to a variety of consumer-grade technology brought in by the employees.



 Companies that don’t protect themselves through policies place themselves at risk.
Companies that don’t protect themselves through policies place themselves at risk.






