How secure is Mobile Device Management anyway?
January 8, 2014 7 Comments
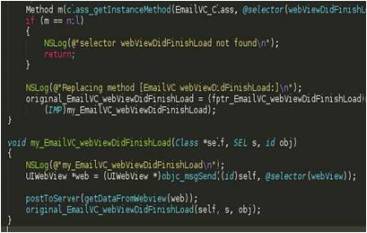 Researchers have successfully breached the Good Technology container. MDM software can only be as secure as the underlying operating system.
Researchers have successfully breached the Good Technology container. MDM software can only be as secure as the underlying operating system.
As the adoption of smartphones and tablets grows exponentially, one of the biggest challenges facing corporate IT organizations is not the threat of losing the device – likely owned by the employee – but the threat of a targeted attack stealing sensitive corporate data stored on these mobile devices. As a first line of defense, an increasing number of companies rely on Mobile Device Management software and Secure Container solutions to secure and manage corporate data accessed from these mobile devices. However, a recent analysis conducted by Lacoon Mobile Security – presented a few weeks ago at the BlackHat conference in Amsterdam – shows that the leading secure container solution Good Technology can be breached and corporate email stolen from Apple iOS and Android devices.



 One of the less understood aspects of Consumerization is its financial impact on the business. Is your BYOD program in the money?
One of the less understood aspects of Consumerization is its financial impact on the business. Is your BYOD program in the money? Google recently announced Android 4.1 ‘Jelly Bean’ at its I/O conference in San Francisco. The latest flavor of the world’s #1 mobile OS promises better user experience and sexier UI. But does it really make any easier for IT to secure and manage those
Google recently announced Android 4.1 ‘Jelly Bean’ at its I/O conference in San Francisco. The latest flavor of the world’s #1 mobile OS promises better user experience and sexier UI. But does it really make any easier for IT to secure and manage those Where employees once enquired about private medical cover and company cars, now they may ask to work on their own iPhone or Android. It’s a perk of the job that can boost productivity, but implement your BYOD policy incorrectly (or even pretend it’s not happening) and it could cost you dear, say our experts
Where employees once enquired about private medical cover and company cars, now they may ask to work on their own iPhone or Android. It’s a perk of the job that can boost productivity, but implement your BYOD policy incorrectly (or even pretend it’s not happening) and it could cost you dear, say our experts




